Reflection Amplification Vectors: a Chronology - Link 11 - Take your cybersecurity to the next level

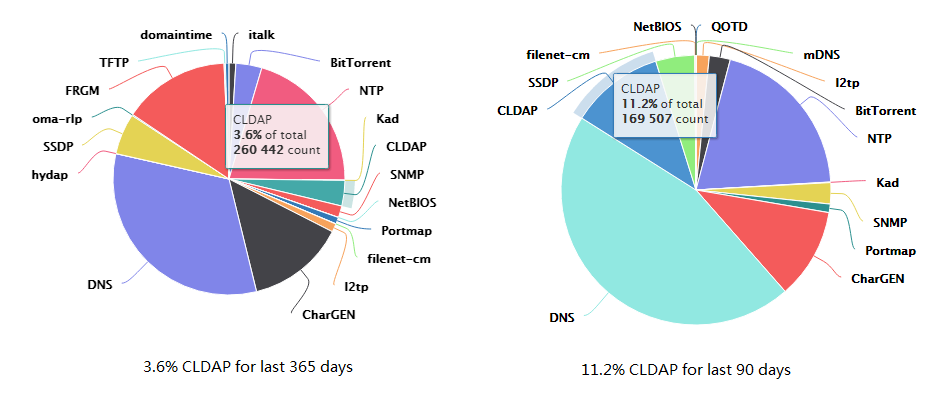
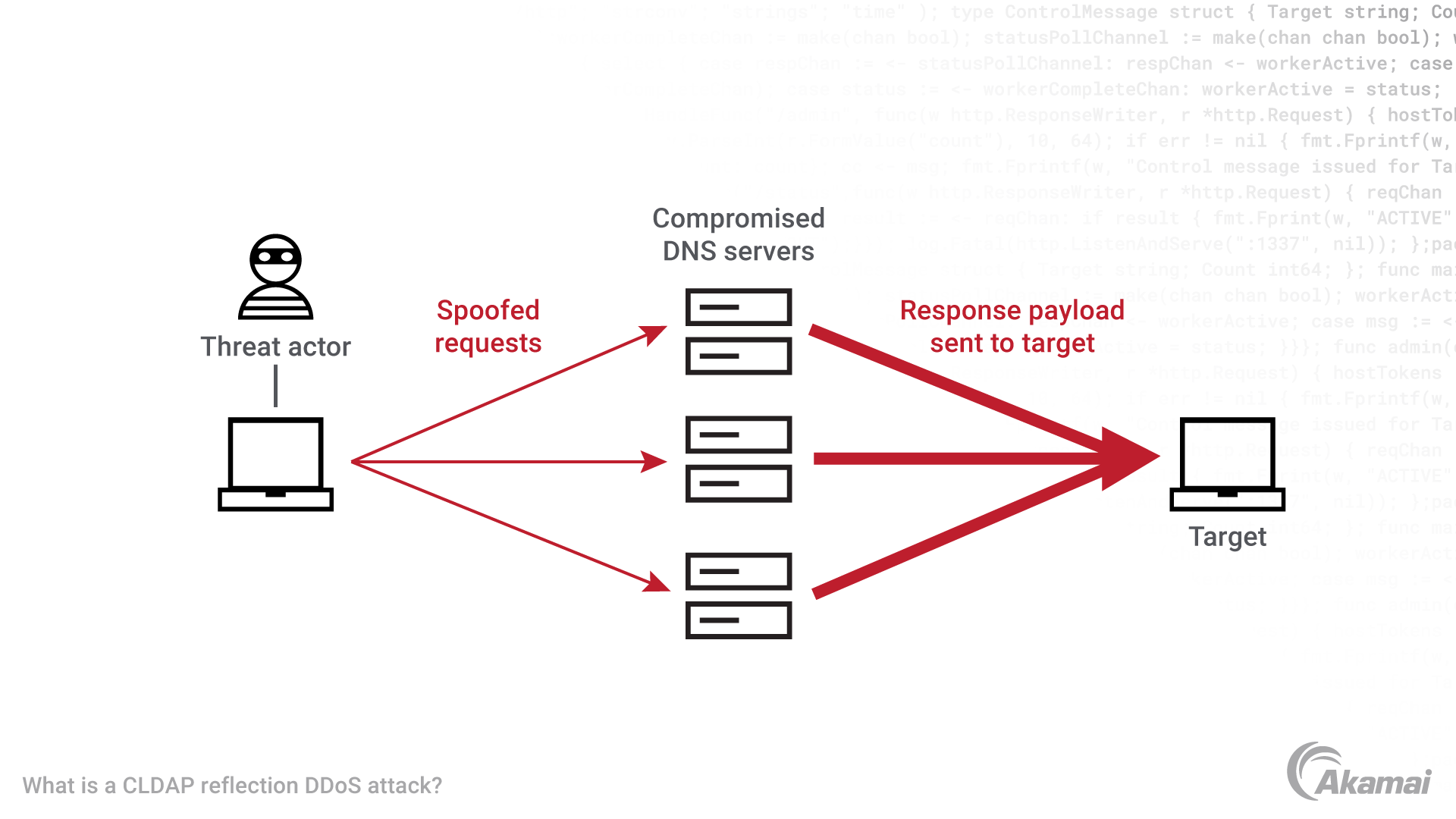
A study on reduction of DDoS amplification attacks in the UDP-based CLDAP protocol | Semantic Scholar
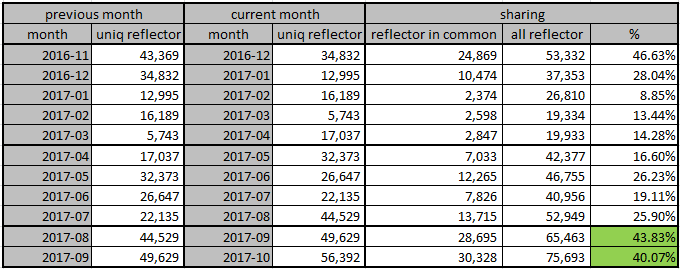
ZoomEye Report: Global Detection and Analysis of Amplified Reflection DDoS Attacks | by Knownsec 404 team | Medium